жЬАеЊМжЫіжЦ∞: 2020-10-14
зЫЃйМД
AWS = Amazon Web Services
cli tools
- Euca2ools (EPEL)
- Ansible (Python, Playbooks)
- ec2-ami-tools.noarch.rpm (yum install java-1.7.0-openjdk)
- aws (https://aws.amazon.com/cli/)
зФҐеУБдїЛзіє
- VPC
- EC2
-
EBS(Elastic Block Store)
- network-attached, and persist independently from the life of an instance)
- жФѓжПіеїЇзЂЛ snapshots - AMI (Amazon Machine Image)
- S3
- IAM (Identity and Access Management)
и°Уи™Ю
- AMI (Amazon Machine Images)
- VPC (Virtual Private Cloud )
CloudShell
persistent storage of 1 GB for each AWS Region # 120 days after the end of your last session
Shell sessions (Inactive sessions: 20~30 mins)
Long-running sessions: 12 hours automatically end (even if the user is regularly interacting with it)
AMI
Ubuntu AMI
http://cloud-images.ubuntu.com/locator/ec2/
Centos-AWS
http://wiki.centos.org/Cloud/AWS
Debian
https://wiki.debian.org/Cloud/AmazonEC2Image
Account info.
AWS Account Number (12 digit number)
User ID ( 12 digit number )
Access Key ID (20 alpha-numeric )
Secret Access Key (40 alpha-numeric-slash-plus)
X.509 Certificate and Private Key
( AWS API (SOAP only))
жЯ•зЬЛ Access Key ID еПК Secret Access Key
Web Panel: http://aws.amazon.com/console/
"account"-> security credentials -> Access Keys -> 'Show Access Key' link
# Note: You can have a maximum of two access keys (active or inactive) at a time.
# My Account -> Usage Reposts
IAM зФ®еЬЦ
Portal
https://console.aws.amazon.com/iam
и®≠еЃЪ Security Status
- Root Account MFA
- Password Policy
- и®≠еЃЪ Permission
MFA - Multi-Factor Authentication
- MFA device
- Virtual MFA Device (Google Authenticator) # Price Free
и®≠еЃЪ Permission
attach the created policy to the IAM group or role to which the IAM user is assigned.
For EC2, you must consider two questions when locking down a user's EC2 access to a single virtual private cloud (VPC):
-
Which API actions support Amazon Resource Names (ARNs) and conditions?
Action: "ec2:DescribeInstances"
Resource types: arn:${Partition}:ec2:${Region}:${Account}:instance/${InstanceId} # instance - Which API actions do not support ARNs and conditions?
Example
View_Instances_CloudWatch_Metrics
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": [
"ec2:DescribeInstances",
"cloudwatch:DescribeAlarms",
"cloudwatch:GetMetricStatistics"
],
"Resource": "*"
}
]
}йЩРеИґ A/C жЯ•зЬЛеИ∞дїАйЇЉ Instanse
The Amazon EC2 "ec2:Describe*" API actions do not support resource-level permissions,
so you cannot control which individual resources users can view in the console.
Therefore, the * wildcard is necessary in the Resource element of the above statement.
иІ£ж±ЇжЦєж°И: Organizations
https://console.aws.amazon.com/organizations/
Veeam iam restore permission
https://helpcenter.veeam.com/docs/backup/vsphere/restore_amazon_permissions.html
Free tier
* дЄАеЃЪи¶БзФ®дњ°зФ®еН°ж≥®еЖК, дєЛеЊМжЬГжЬЙ USD$1 и≤їзФ®
ењЕ詶й†ЕзЫЃ:
- EC2
- AWS Data Transfer
- EBS
- EFS
- ELB
- CloudFront
- S3
- ElastiCache
- CloudWatch
- Elastic Container Registry
- RDS
- DynamoDB
и©≥и¶Л: Link
12 Month (Per Month) Free
* Free зЪД Service дЄНеП™дї•дЄЛйАЩдЇЫ
EC2
750 hours of Amazon EC2 Linux Micro Instance (t3.micro)
=> дЄНжШѓжЙАжЬЙ instanse йГљдњВ free зЪД, еП™жЬЙ Micro Instance жЙНжШѓ Free
* If you stop and start an EC2 instance three times in an hour,
you’ll have used up three hours of your free-tier allotment.
AWS Data Transfer
100 GB/mo
(includes: EC2 S3, ELB)
EBS
- 30 GB of Amazon Elastic Block Storage
- 2 million I/Os
- 1 GB of snapshot
EFS
- 5 GB
ELB
- 750 hours of an Elastic Load Balancer
- 15 GB data processing
- 15 LCUs
CloudFront
- 1 TB of Data Transfer Out
- 10,000,000 HTTP or HTTPS Requests
- 2,000,000 CloudFront Function Invocations
S3
- 5 GB of Amazon S3 standard storage
- 20,000 Get Requests
- 2,000 Put Requests
ElastiCache
-
750 hours of Amazon ElastiCache
(Redis / Memcached)
CloudWatch
- 10 Amazon Cloudwatch metrics
- 10 alarms,
- 1,000,000 API requests
- 5GB of Log Data Ingestion and 5GB of Log Data Archive
* Basic Monitoring metrics (at five-minute frequency) for Amazon EC2 instances are free of charge)
Elastic Container Registry
- 500 MB-month
RDS
- MySQL, PostgreSQL, MariaDB, or SQL Server
- 750 Hours of Amazon RDS Single-AZ db.t3.micro
- 20 GB of General Purpose (SSD) database storage
- 20 GB of storage for database backups and DB Snapshots
DynamoDB
- 25 GB of Storage
- 25 provisioned Write Capacity Units (WCU)
- 25 provisioned Read Capacity Units (RCU)
жЯ•зЬЛ Free tier еИ∞еєЊжЩВ:
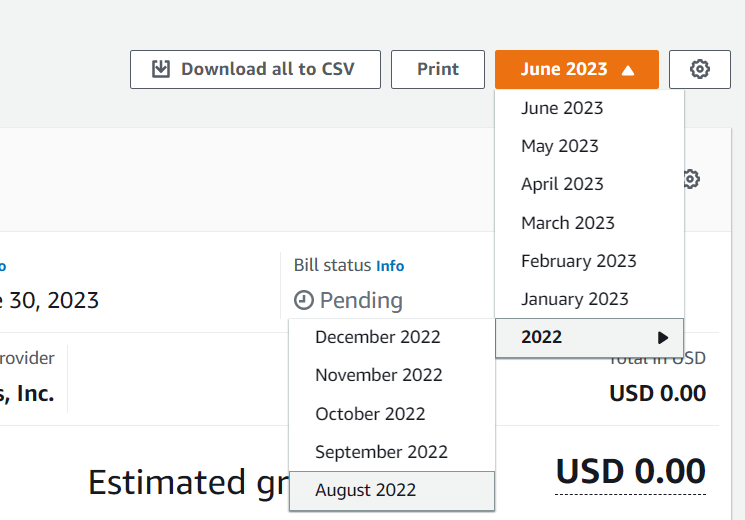
Account > Billing dashboard > Bills
Click on the “Date” and scroll down to the last date, which is the account creation date
зФ®йЗП
жЯ•зЬЛдљ†жЬЙдїАйЇЉеЬ®зФ®
еЬ®еЈ¶дЄКиІТзЪД My Account / Console -> Account Activity
Usage Reports
еЬ®еЈ¶дЄКиІТзЪД My Account / Console -> Usage Reports
EC2 Reachability Test
http://ec2-reachability.amazonaws.com/
Estimate AWS latency
[1] By ping IP
HK to X (@201904)
US-east: 230 ms US-west: 160 ms Singapore: 40 ms JP: 55 ms
[Web]
https://www.cloudping.info/
Route tables
Each subnet in your VPC must be associated with a route table, which controls the routing for the subnet (subnet route table).
local route
Every route table contains a local route for communication within the VPC.
This route is added by default to all route tables.
If your VPC has more than one IPv4 CIDR block,your route tables contain a local route for each IPv4 CIDR block.
(You cannot modify or delete these routes)
Main route table
The route table that automatically comes with your VPC.
It controls the routing for all subnets that are not explicitly associated with any other route table.
Custom route table
A route table that you create for your VPC.
Subnet route table
A route table that's associated with a subnet.
Gateways
Internet Gateway(igw)
The Amazon VPC side of a connection to the public Internet.
- perform one-to-one NAT for instances that have been assigned public IPv4 addresses.
Tasks
Creating a subnet
Creating and attaching an internet gateway
Creating a custom route table
- For IPv4 traffic, specify 0.0.0.0/0 in the Destination box, and select the internet gateway ID in the Target list.
Creating a security group for internet access
- By default, a VPC security group allows all outbound traffic.
You can create a new security group and add rules that allow inbound traffic from the internet.
Adding Elastic IP addresses
NAT gateways
Pricing: hourly usage and data processing rates apply
- Price per NAT gateway ($/hour) US$0.065@2020 # Region: HK
- Price per GB data processed ($) US$0.065@2020 # Region: HK
Each NAT gateway is created in a specific Availability Zone and implemented with redundancy in that zone.
If you have resources in multiple Availability Zones and they share one NAT gateway
The Elastic IP address cannot be changed after you associate it with the NAT Gateway.
Deleting a NAT gateway disassociates its Elastic IP address, but does not release the address from your account.
You cannot associate a security group with a NAT gateway.
You can use security groups for your instances in the private subnets to control the traffic to and from those instances.
Migrating from a NAT instance to NAT gateway
Private IP
An instance's private IP address will never change during the lifetime of that instance.
Re-assign private IP to new instance
If you have an existing instance with the private IP you want (EXAMPLE: 10.0.0.101).
You should take an image (AMI) and then terminate that instance. Because it is in a VPC, just stopping it won't free the private IP.
Once you have a good image, terminate it. That would free up its Private IP Address. Thus you would have (10.0.0.101) available
Then assign a secondary private IP to your new instance that you want and specify the private IP to be the one you want it to be (10.0.0.101)
1. Open EC2 dashboard. 2. Click on Launch Instance. 3. Then choose My AMIs on the left side tab and select your AMI. 4. Select the desired instance type. 5. Click on "Next :Configure Instance details". 6. Then select/provide the VPC ID and choose the subnet in network and subnet field respectively. 7. Select "disable" option in " Auto-assign Public IP" field of "Configure Instance" (which is third step of launching an instance) 8. In the same page, scroll down and click on Network Interfaces. 9. Then paste the required private IP in Primary IP field. 10. Add storage, configure Security group if required ( if you wish) 11. Click on Launch.
Assigning a public IPv4 address during instance launch
EC2-Classic: automatically assigned a public IP address to the instance (This behavior cannot be modified.)
If an instance is launched in a VPC, you control whether it receives a public IP or not
VPC:
Each subnet has an attribute that determines whether instances launched into that subnet are assigned a public IP address.
- To access the public IP addressing feature when launching an instance
- To enable or disable the public IP addressing feature using the command line
Elastic IP Pricing
By default Amazon Web Services allows each AWS account to have up to five Elastic IP addresses.
If you need reserve more than five Elastic IPs, you must submit a request for more Elastic IPs to Amazon.
An Elastic IP address doesn’t incur charges as long as all the following conditions are true:
- The Elastic IP address is associated with an EC2 instance.
- The instance associated with the Elastic IP address is running.
- The instance has only one Elastic IP address attached to it.
Security Group & Network ACLs
Diagram
Internet
||
\/
-------------------------
| Network ACLs |
-------------------------
SG SG
|Instance-A | Instance-B|
Network ACLs
* Operates at the subnet level
* Supports allow rules and deny rules
(process rules in order, starting with the lowest numbered rule)
* stateless
Security Group
* Operates at the instance level
* Supports allow rules only
* stateful
When you launch an instance in a VPC, you can assign up to five security groups to the instance.
You can have 50 inbound and 50 outbound rules per security group
Windows 's Agent
- Amazon SSM Agent(amazon-ssm-agent.exe)
- AWS Lite Guest Agent
Amazon SSM Agent(amazon-ssm-agent.exe)
AWS Systems Manager Agent makes it possible for Systems Manager to update, manage, and configure these resources.
The agent processes requests from the Systems Manager service in the AWS Cloud,
and then runs them as specified in the request.
SSM Agent then sends status and execution information back to the Systems Manager service by
using the Amazon Message Delivery Service (service prefix: ec2messages)
To automatically update SSM Agent
Open the AWS Systems Manager console at https://console.aws.amazon.com/systems-manager/
In the navigation pane, choose Managed instances.
Choose Agent auto update.
AWS Lite Guest Agent
The Lite Agent is a component of the AWS PV Driver package which is specifically responsible for handling Shutdown and Restart events from AWS APIs.
However, this agent is not used on Nitro platform based instances (T3/M5/C5/R5, etc.) and as such, can be safely disabled.
This is because, Nitro based instances use ACPI signals to perform the Reboot and Shutdown events.
(https://aws.amazon.com/ec2/nitro/)
In case you want to disable the service, you can run the following commands in powershell:
PS C:>Set-Service AWSLiteAgent -StartupType Disabled PS C:>Stop-Service AWSLiteAgent
AWS PV Drivers(Windows drivers)
OS: s2008R2 ~ s2019
These drivers are used by Amazon EC2 to map instance store and Amazon EBS volumes to their devices.
The AWS PV drivers are stored in the "%ProgramFiles%\Amazon\Xentools" directory.
Command line tool, xenstore_client.exe, that enables you to access entries in XenStore
The AWS PV driver components are listed in the Windows registry under
"HKLM\SYSTEM\CurrentControlSet\Services"
These driver components are as follows:
xenbus, xeniface, xennet, xenvbd, and xenvif.
Version
8.3.3@(4 February 2020)
Upgrade
https://s3.amazonaws.com/ec2-windows-drivers-downloads/AWSPV/Latest/AWSPVDriver.zip
* Upgrade еЃМеПѓиГљжЬГж≠їж©Я, жЙАдї• upgrade еЙНдЄАеЃЪи¶Б Backup !!
еЕґдїЦ
![й¶Цй†Б Logo ґгЅ¬ Keith ≥]≠p !!](/themes/mytheme/logo.png)